Chrome Extension Used to Spam You After Developer Gives Up Credentials to Cybercriminals
By: Jim Stickley and Tina Davis
August 17, 2017
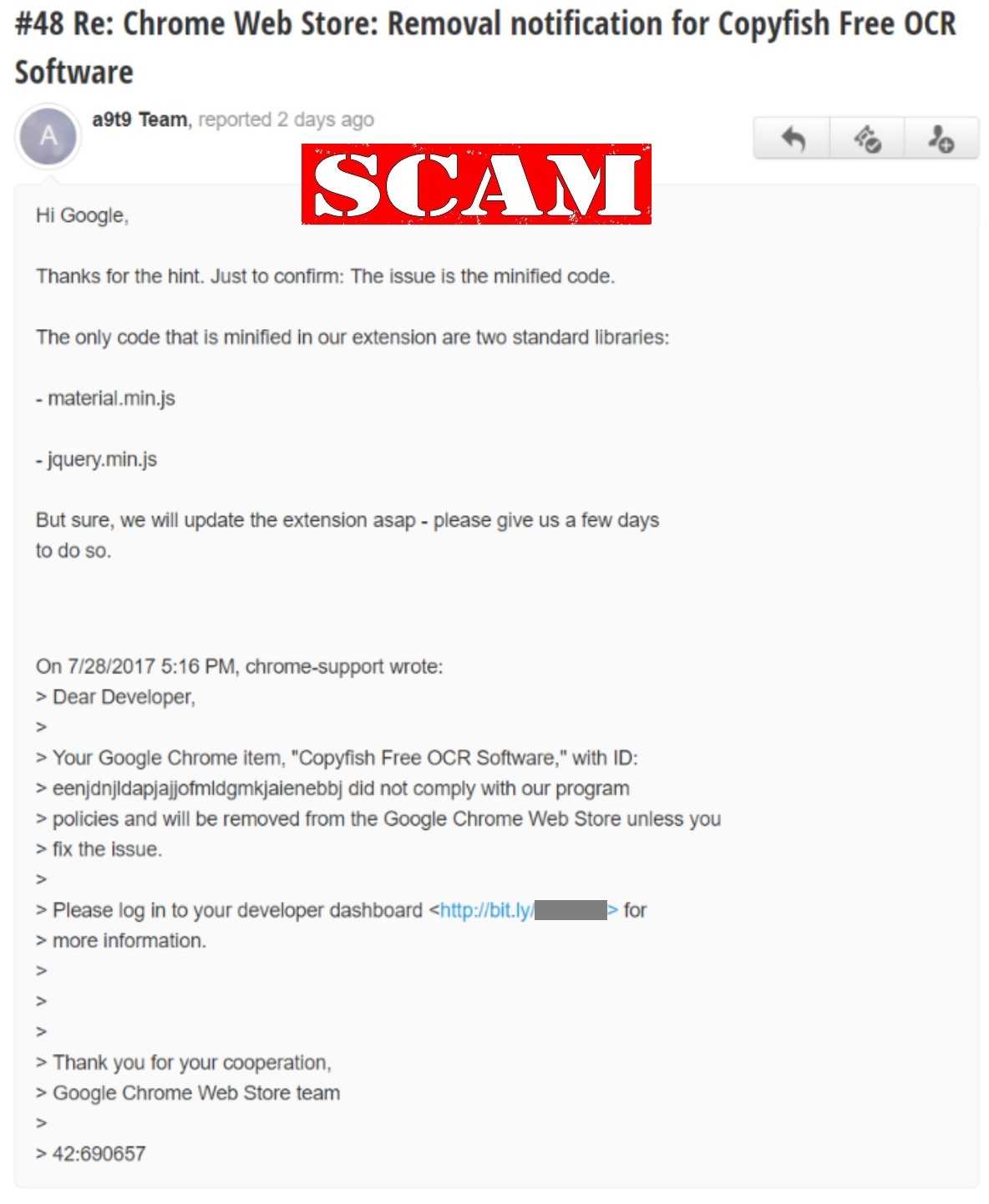
It’s a typical day at the office and you arrive at your desk. You get your coffee, greet your colleagues, head back to your desk, open your email and start reading. You see a message in the list from Google. The message alerts you that the extension you created needs to be updated or it will be removed from the Google Web Store. There is a link inside the message. You click it and sign in to your Google account without a second though. But uh oh.
Yep, that was a phishing attack and now the cybercriminals have your developer credentials that take them right to the Copyfish OCR browser extension that your company, A9t9 created. They didn’t improve it either. Instead, they added spam and advertisements into websites using that extension.
 This did happen and it shows that even technology professionals can get tricked sometimes. There are some guidelines that everyone can follow to prevent falling victim to such scams:
This did happen and it shows that even technology professionals can get tricked sometimes. There are some guidelines that everyone can follow to prevent falling victim to such scams:
- Be very aware that links can cause trouble – It's better to manually enter a website's URL directly into the address bar than to click on a link if you think it’s legitimate. You may want to do a quick check by hovering over the link with the mouse pointer first. If it goes to a location that seems a bit odd, just delete the message.
- Typos are still a good indicator of phishing attacks – Although the scammers are certainly getting much better at fooling us, they still make typos and grammatical mistakes. Messages from reputable organizations usually are checked and checked again for these mistakes before a message makes it to your inbox.
- Take advantage of two-factor authentication whenever possible – Two-factor authentication (2FA), two-step verification, or multi-factor authentication (MFA) requires you take multiple steps to authenticate yourself before you get access to your account. Often this means you will receive a text with a randomly generated code that you have to enter before getting access. Sometimes you will get a key fob with those codes. Some sites such as Google and Dropbox also allow you to use the security key method. If you have the choice to enable any of these, do so.
- Install and keep security software updated on all devices – Having strong protection on all of your internet-connected devices is no longer optional. While it will not guarantee you never have to do your own analysis of a message, popup dialogue, or website, it is a great first line of defense for your personal devices.
The employee in this story gave up very important credentials indeed. The attackers were able to use them and move the Copyfish product to their own developer account and have their way with it.
If you had planned to download OCR software, don’t use this one. The company has not yet been able to get the product back into their own Google developer account. Do some research and find another one.